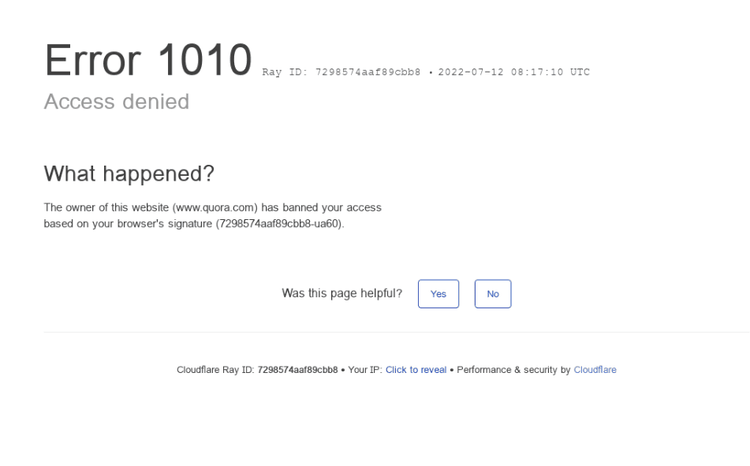
What Is Error 1010 by Cloudflare
Cloudflare throws Error 1010 when your web client's signature or fingerprint is on the website's ban list. That can happen when trying to bypass the Cloudflare anti-bot system using HTTP clients like Requests, Axios, etc. These tools have unique signatures that are easily identifiable as bots. The same applies to headless browsers like Selenium or Puppeteer.
Let's see how to overcome this error.
How to Avoid Error 1010 from Cloudflare
To avoid Error 1010 from Cloudflare, you must hide your fingerprint or emulate an actual web browser. Here are three ways you can achieve that:
1. Run JavaScript with a Browser
One way to emulate an actual browser is by running JavaScript. If your web scraper can't execute it, it can easily be detected as a bot.
Headless browsers like Puppeteer, Selenium, and Playwright enable web scrapers to automate browser tasks and render JavaScript like a real user. That could help you avoid Cloudflare Error 1010. To learn more, check out our guide on the best headless browsers for web scraping.
However, browser automation tools possess properties that make them easy to fingerprint and identify. So, for better results, fortify your headless browsers against JavaScript fingerprinting with plugins like Undetected ChromeDriver for Selenium.
2. Rotate Headers
Cloudflare can identify web scrapers based on their User Agent headers. If you have a non-browser UA, as HTTP clients do by default, that will give you away.
Some headless browsers have the same issue, like HeadlessChrome is stated in its User Agent. You can avoid Cloudflare Error 1010 by customizing and rotating your UAs to make your requests appear from different users.
However, using real and correctly-formed User Agents is important, otherwise you might get blocked. Check out our guide on Python Requests User Agents to learn more and get well-formed ones.
3. Use a Web Scraping API
The previous methods won't work in many cases, especially against modern websites with advanced anti-bot detection systems, so you might still get Cloudflare Error 1010. Moreover, implementing them requires higher technical knowledge and resources, making it difficult to scale. For a more streamlined and effective solution, use web scraping APIs.
ZenRows is an all-in-one web scraping API that helps you bypass Cloudflare and all other anti-bot challenges. With a single API call, you can rotate headers and retrieve the needed data while avoiding technical challenges. Sign up to get 1,000 free API credits to try ZenRows.
Frequent Questions
What Is Error Code 1010 from Cloudflare?
Error code 1010 from Cloudflare indicates the website owner has implemented a blocklist for specific browser signatures, and your web client is on that list. That might happen when using common tools, like Selenium headless browser, since those share fingerprints.
Did you find the content helpful? Spread the word and share it on Twitter, or LinkedIn.