Kasada is actually one of the most frustrating anti-bot measures for scrapers. But after so much research, we've come up with the top three ways to break through its defenses.
- Method 1: Bypass Kasada with a Web Scraper API.
- Method 2: Rotate Real Request Headers.
- Method 3: Bypass Kasada with Fortified Headless Browsers.
But first, let's understand what we're dealing with.
What Is Kasada?
Kasada is a Web Application Firewall (WAF) with advanced bot detection techniques. What it does is to act as a proxy between your request and the destination server. That way, it can monitor and filter every incoming request. Unfortunately, it also blocks web scrapers during its operation.
Kasada detects bot traffic by analyzing differences in configuration and behavior between bots and legitimate users. Unlike other WAFs, Kasada doesn't show you a CAPTCHA. That said, it's more aggressive because it challenges every request to the destination web server. This can pose challenges during scraping if your traffic is identified as bot-like.
Indicators of Kasada Protection
One way to know whether you're getting blocked by Kasada protection is to watch out for response headers like x-kpsdk-ct, x-kpsdk-r, or x-kpsdk-c. These header strings often accompany Kasada's challenges and responses, providing unique identifiers that help track client verification attempts.
The Kasada challenge also often blocks scrapers with a Kasada 403 forbidden error. It may also return a 429 "Too Many Requests" error response due to rate-limiting, which you can overcome by retrying failed requests using best practices.
While these are the most common, keep in mind that response codes may still vary between 400 and 500. The 400+ status codes may indicate Kasada client-side detection, while 500+ codes potentially indicate server-side issues, which can be trickier and more challenging to bypass.
Now, let's look into how it detects bots so we can better navigate around its defenses.
How Does Kasada Detect Bots?
Kasada deploys multiple sophisticated methods to identify and block bot traffic. Understanding these bot detection techniques is crucial to successfully bypassing them.
1. IP Address Reputation
Kasada assesses the reputation of an IP address to determine its trustworthiness. If your IP address has been involved in scraping activities or triggered anti-bot mechanisms in the past, Kasada is likely to block it.
Even if you rotate multiple IP addresses, data center IPs are particularly vulnerable to detection since regular users don't use them. So Kasada's system can easily flag them as suspicious.
Switching to high-quality residential proxies or mobile IPs can help bypass Kasada's IP detection, as these IPs appear more like those of genuine users and have good trust scores. However, rotating the IPs too frequently or predictably could raise suspicion, especially when dealing with an advanced anti-bot mechanism like Kasada.
2. TLS Fingerprinting
Kasada also uses TLS (Transport Layer Security) fingerprinting to differentiate legitimate users from bots. TLS is a cryptographic protocol designed to secure communication over a network. It ensures that the data transmitted between the client and the server is encrypted, maintains data integrity, and verifies the identities of communicating parties through certificate exchange.
Communication between the client and the server begins with a TLS handshake. During the TLS handshake, both parties evaluate factors like the supported cipher suites, TLS versions (1.2 or 1.3), and supported extensions. Once the web server and the client agree on these values, Kasada creates a unique fingerprint for each connection to identify the client.
This fingerprint is compared against a list of trusted fingerprints. If any discrepancies are found, the connection may be flagged. Most web scraping tools can establish TLS connections, but they often fail to mimic subtle variations that human browsers use, making them easier to detect.
3. HTTP Details
Kasada inspects HTTP headers, such as User Agent and Referer, to gauge whether the request is from a legitimate browser.
Kasada evaluates incoming requests by comparing them to a database of known bot header signatures or checking them against the website's predefined header policies. Any discrepancies in the header values can lead to detection and blocking. Since browsers generally send headers in a specific sequence, requests with headers that appear out of order can reveal the presence of a web scraper.
Missing or inconsistent headers can also quickly expose your request as automated. Additionally, older HTTP versions (e.g., HTTP/1.1) can raise red flags since most modern browsers now use HTTP/2 or HTTP/3.
To minimize the risk of detection through HTTP analysis, ensure your requests include the appropriate headers commonly expected during web scraping. Additionally, you should opt for HTTP clients that support modern protocols like HTTP/2 or higher for improved stealth and performance.
4. JavaScript Fingerprinting
JavaScript fingerprinting involves running scripts in the user's browser to gather specific data and create a unique client signature. Kasada uses this technique to assess whether the client can accurately execute JavaScript, as many bots struggle with complex client-side operations.
Various details are collected during fingerprinting, including browser navigator fields, host device specifications, runtime properties, and hardware capabilities. Any deviations from expected values, improper execution, or noticeable delays can signal bot-like behavior and result in blocks.
Since JavaScript fingerprinting occurs on the client side, bypassing it often involves reverse engineering the script to understand its logic or using advanced headless browsers configured to mimic real user environments.
5. Behavior Analysis
Human interactions tend to be dynamic. A human user might scroll in unpredictable bursts, pause, or click in varied sequences.
An automated script typically maintains a static behavioral pattern, such as scrolling the same height several times, clicking the same element multiple times, navigating multiple web pages simultaneously, or even filling a form within milliseconds.
Kasada detects bot behavior by flagging these overly consistent or repetitive actions. It compares these actions to what a real user might do to spot any inconsistencies and block suspicious activities.
Now that we know how Kasada identifies web scraping activities. Let's explore how to bypass its detection with proven methods.
1. Bypass Kasada With a Web Scraping API
The easiest way to overcome Kasada's security barriers during web scraping is by using web scraping APIs. A standout choice is ZenRows' Universal Scraper API, which offers all the features needed to bypass even the most sophisticated anti-bots like Kasada effortlessly and at scale.
The scraper API handles fingerprint evasion, premium proxy rotation, JavaScript execution, and header management for you. This way, you can concentrate on extracting data without dealing with complex technical details. ZenRows is especially easy for beginners, requiring only a single API call in your chosen programming language to get started.
Let's see how it works by scraping the full-page HTML of Canada Goose, a Kasada-protected website.
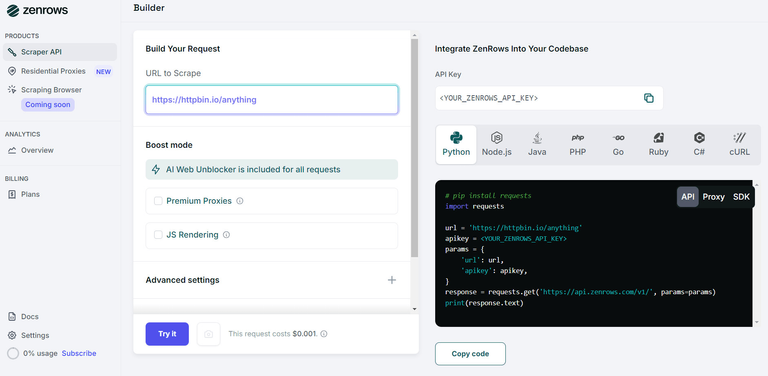
Sign up for free to open the Request Builder. Paste the target URL in the link box, and enable Premium Proxies and JS Rendering. Next, select your programming language (Python, in this case) and choose the API connection mode. Then, copy and paste the generated code into your scraper file.
Here's how the generated Python code looks:
# pip install requests
import requests
url = "https://www.canadagoose.com/"
apikey = "<YOUR_ZENROWS_API_KEY>"
params = {
"url": url,
"apikey": apikey,
"js_render": "true",
"premium_proxy": "true",
}
response = requests.get("https://api.zenrows.com/v1/", params=params)
print(response.text)
The output will display the complete HTML of the protected site:
<html lang="en-CA">
<!-- ... -->
<title>
Luxury Performance Outerwear & Clothing | Canada Goose CA
</title>
<meta name="description" content="Since 1957, Canada Goose crafts performance luxury outerwear & clothing. Discover year-round essential styles like winter jackets, light down puffers, footwear & more.">
<!-- ... -->
</html>
Pretty simple, right? In just a few lines of code, you've scraped a Kasada-protected website using the ZenRows web scraping API.
While this approach is ideal for a quick and efficient solution, there are other methods if you prefer a more hands-on approach.
2. Rotate Real Request Headers for Kasada Bypass
Kasada pays close attention to HTTP headers like User Agent, Referer, and Accept-Language. These headers make a request resemble one from a real browser, and Kasada's detection system will flag anything that looks unusual.
Rotating your headers involves using various User Agent strings, rotating them frequently, ensuring that other headers align with the User Agent in use, etc. For instance, if you're using a Chrome User Agent, the headers should reflect Chrome-specific details and must be updated regularly to match the latest browser versions.
However, managing headers manually can become a challenge at scale. Keeping track of ever-changing User Agents and maintaining correct header combinations can be time-consuming, and any inconsistency can quickly lead to detection and blocking. ZenRows can automate header rotation, making it easy for you to stay undetected.
3. Bypass Kasada With Fortified Headless Browsers
Browser automation tools like Puppeteer, Playwright, and Selenium can simulate real user interactions, execute JavaScript, and run in headless or full-browser modes. However, standard versions of these tools are often easily detected because they expose bot-like characteristics, such as the HeadlessChrome flag or the presence of WebDriver.
Using a fortified headless browser modifies the common markers that anti-bot systems look for, making it harder for detection systems like Kasada to identify your scraping activity. Popular fortified options include:
- Puppeteer Stealth: Stealth plugin with anti-bot evasions for Puppeteer.
- Playwright Stealth: Stealth plugin with anti-bot evasions for Playwright.
- SeleniumBase and Undetected ChromeDriver (UC): Enhances Selenium to avoid detection markers.
While these fortified browsers have custom tweaks to avoid detection, they are not ideal for large-scale web scraping. Running multiple browser instances consumes significant memory, and despite the tweaks, they may still leave detectable traces over time.
Using ZenRows Scraping Browser as an add-on for Puppeteer and Playwright allows you to access hundreds of websites, eliminating the need for expensive cloud setups and time-consuming maintenance. This simplifies scaling and running high-volume scraping operations while enhancing your automation's overall stealth.
Conclusion
While manual bypass methods can be effective, they often become unreliable when scaling up. Kasada's regular updates make these approaches a constant maintenance burden. That's because they require significant time investment and technical expertise.
The most reliable solution is to use ZenRows' web scraping API, which provides an all-in-one toolkit for bypassing Kasada without limitations. This solution gives you access to any Kasada-protected website with a single API call. ZenRows handles all the complexities of fingerprinting evasion, premium proxy rotation, JavaScript execution, actual user spoofing, request header management, and all other anti-bot and CAPTCHA bypass mechanisms.
Try ZenRows for free today without a credit card!